Useful Tools for security and networking
Useful ToolDescriptionPiriform's CCleanerThis is a great utility that will scrub your system clean.CPUID's CPU-ZThe utility to find out the specs of the CPU on your...
Protected: Security and Risk Management
Security management encompasses the administrative, technical and physical controls necessary to adequately protect the confidentiality, integrity, and availability which is known as the CIA Triad of information assets.
Common Ports and Their Associated Protocols in Networking
Port Number
Associated Protocol (or Keyword)
TCP/UDP Usage
Secure Version and Port
Usage
21
FTP
TCP
FTPS, port 989/990
Transfers files from host to host.
22
SSH
TCP or UDP
Secure Shell: Remotely administers network devices and systems. Also used by Secure Copy...
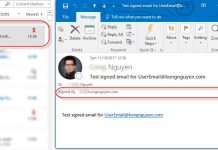
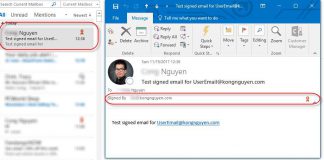
Secure your email by using a digital signature
Secure your email by using a digital signature is an option to make your email more secure. A digital signature isn't the same as a...