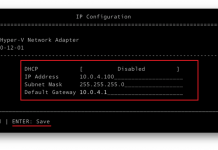
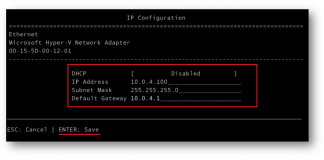
Configuring a Nano Server
Once you have deployed the VHDX image in a Nano VM and started it. Now it's time to log on and configure the basic settings of the VM.
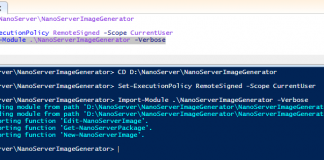
Deploying a Nano Server
As you know, there is no wizard for installing Nano Server, like Windows Server and Server Core. You install it by creating a Virtual...
Common Ports and Their Associated Protocols in Networking
Port Number
Associated Protocol (or Keyword)
TCP/UDP Usage
Secure Version and Port
Usage
21
FTP
TCP
FTPS, port 989/990
Transfers files from host to host.
22
SSH
TCP or UDP
Secure Shell: Remotely administers network devices and systems. Also used by Secure Copy...
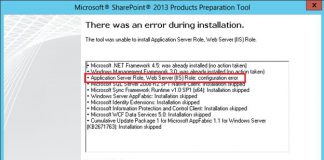
SharePoint 2016 Prerequisites fails while installing Windows Server AppFabric
When installing SharePoint Server 2016 on either Windows Server 2016 standard or 2012 R2 Standard. There is a common issue with Windows Server AppFabric. The...
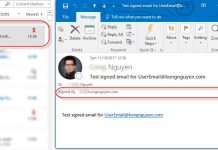
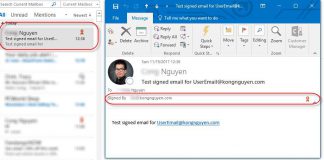
Secure your email by using a digital signature
Secure your email by using a digital signature is an option to make your email more secure. A digital signature isn't the same as a...
Create a Free Dynamic DNS with No-IP
Sign up a free account
Go to No-IP website sign up link: https://www.noip.com/sign-up.
Enter your email and password in box 1 and 2.
Select a...
Install SQL Server 2014 SP2 for SharePoint Server 2016
This is part of Install SharePoint Server 2016 article
The following is step by step pictures which demonstrate how to install SQL Server 2014 SP2 for SharePoint Server...
Install SharePoint 2016 Step by Step
This is part of Install SharePoint Server 2016 article
The following is step by step pictures which demonstrate how to install SharePoint Server 2016 on a server
Install SharePoint Server...
Create a Dynamic DNS with Google
If your domains are hosted at Google, you have a free option to create a Dynamic DNS with Google Domains registrar.
Step 1: Go to https://domains.google ⇒ Log...
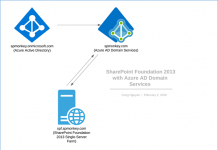
Install SharePoint Server 2016
Install SharePoint Server 2016 on Server 2016 Standard with SQL Server 2014 SP2
This post is a quick note of step by step when I install...